Dataprotector : IDB Maintenence
.1 IDB Backup
Make sure all Data Protector production backups have completed overnight. Any backups that need to be re-run should be re-run before the backup of the IDB is taken. It would also be worth making sure there is no known requirement for a Data Protector restore. Disable all backups scheduled to run before 6pm.
Note: Timings listed on this document are approximate, based on previous run times. Depending on the condition of the Data Protector IDB and available resource on the Cell manager, times could differ. Though it’s expected regular purge procedures on the DP IDB will decrease job times lower than projected.
Take the following services Offline:
OBVS_MCRS
OBVS_VELOCIS
Copy the Data Protector IDB files from the R:/ of UKSPICDP. These files should be backed up to a local drive.
Once copied, bring the above listed services back online.
1.2 IDB Purge
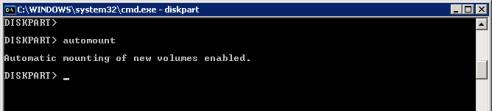
Run the following commands from a command line on the Data Protector Cell manager:
omnidb –strip (seconds)
Omnidbutil –purge –filenames –days 1 -force ( >5 hours)
(This task can take a number of hours, if this task is not finished by early afternoon 3 – 3.30pm, this complete process should be re-run another day)

Note in the above screen shot, this error will be displayed if you try to run another omnidbutil command whilst one is in progress.
To monitor the purge bring up task manager. The rds.exe process is running your purge task.

Omnidbutil –purge –sessions 1 -force (Seconds)
Omnidbutil –purge –DCBF –days 1 -force (Seconds)
Omnidbutil -purge_failed_copies (Seconds)
Create the folder c:\IDBtemp on Cell Manager (If directory already exists delete any existing files)
Run the following commands:
Omnidbutil –writedb –mmdb c:\IDBtemp -cdb c:\IDBtemp (>1 hours)
(This command exports the data base files to a temp folder)
Omnidbutil –readdb –mmdb c:\IDBtemp -cdb c:\IDBtemp (>40 minutes)
(This command re-imports the data, leaving behind purged files)

omnidbutil -remap_dcdir (Seconds)
omnidbutil –fixmpos (Seconds)
omnidbutil -remap_dcdir (Seconds)
omnidbutil -cdbsync ukspicdp (Seconds)
Any Backups disabled before the purge task should be re-enabled.
Perform a test or monitor a production backup to completion to confirm DP is working.
1.3 Stopping purge jobs
Purge jobs should only be cancelled if totally necessary, IE urgent business requirement of a restore/ High impact on Production backups.
If for some reason no up to date backup was taken of the IDB, the job should not be cancelled and procedure completed fully. Disabling a purge job in progress can corrupt the IDB, meaning restoring from an offline backup to get Data Protector operational.
If purge commands do need to be stopped, the following command should be used:
Omnidbutil -purge_stop