This simple PowerShell script will convert your WSUS install from HTTP to HTTPS; simply modify the server fully qualified domain name (FQDN). This is also useful for HTTPS-based System Center 2012 Configuation Manager deployments.
Note that you also require the Execution Policy to be set to RemoteSigned (use the command ‘Set-ExecutionPolicy RemoteSigned’ to change this).
{code lang:css showtitle:false lines:false hidden:false}Import-Module webadministration
Set-WebConfigurationProperty -Filter //security/access -name sslflags -Value “Ssl” -PSPath IIS:\ -Location “WSUS Administration/APIRemoting30”
Set-WebConfigurationProperty -Filter //security/access -name sslflags -Value “Ssl” -PSPath IIS:\ -Location “WSUS Administration/ClientWebService”
Set-WebConfigurationProperty -Filter //security/access -name sslflags -Value “Ssl” -PSPath IIS:\ -Location “WSUS Administration/DSSAuthWebService”
Set-WebConfigurationProperty -Filter //security/access -name sslflags -Value “Ssl” -PSPath IIS:\ -Location “WSUS Administration/ServerSyncWebService”
Set-WebConfigurationProperty -Filter //security/access -name sslflags -Value “Ssl” -PSPath IIS:\ -Location “WSUS Administration/SimpleAuthWebService”
cd “C:\Program Files\Update Services\Tools”
.\WSUSUtil.exe configuressl <server fqdn>
Netsh AdvFirewall Firewall set rule “Windows Server Update Services (HTTPS)” new enable=yes{/code}
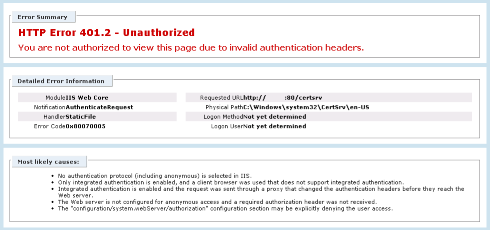
Now browse to the WSUS Administration site in IIS and edit the HTTPS binding to use the correct certificate.